Hackers and Computer Philosophy
Learn the philosophy of the computing world and meet the people who enjoy exploring the details of programmable systems and stretching their capabilities.
All categoriesBooks under this sub-category (17 books)
[No longer freely available] Trapped in the Net: The Unanticipated Consequences of Computerization
Post date: 28 Oct 2004A closer look at how the products of computerization technology have become embedded in all our lives, forcing us to narrow the scope of our choices, our modes of control, and our experiences with the real world.
![[No longer freely available] Trapped in the Net: The Unanticipated Consequences of Computerization](http://www.freetechbooks.com/uploads/1458293273-51uRirLCpSL._SX331_BO1,204,203,200_.jpg)
[No longer freely available] Trapped in the Net: The Unanticipated Consequences of Computerization
Post date: 28 Oct 2004A closer look at how the products of computerization technology have become embedded in all our lives, forcing us to narrow the scope of our choices, our modes of control, and our experiences with the real world.
Blown to Bits: Your Life, Liberty, and Happiness After the Digital Explosion
Post date: 17 Mar 2016Provides a unique and informative perspective from the computing industry's greatest minds. A insightful book that helps you understand computers and their impact on the world in a whole new way.
Publication date: 16 Jun 2008
License: Creative Commons Attribution-NonCommercial-ShareAlike 3.0 Unported
Document Type: Book
Blown to Bits: Your Life, Liberty, and Happiness After the Digital Explosion
Post date: 17 Mar 2016Provides a unique and informative perspective from the computing industry's greatest minds. A insightful book that helps you understand computers and their impact on the world in a whole new way.
Publication date: 16 Jun 2008
License: Creative Commons Attribution-NonCommercial-ShareAlike 3.0 Unported Document Type: Book
Handbook for Bloggers and Cyber-Dissidents
Post date: 29 May 2007A handbook from Reporters Without Borders with handy tips and technical advice on how to to remain anonymous and to get around censorship, and how to establish credibility through observing basic ethical and journalistic principles.
Document Type: Book

Handbook for Bloggers and Cyber-Dissidents
Post date: 29 May 2007A handbook from Reporters Without Borders with handy tips and technical advice on how to to remain anonymous and to get around censorship, and how to establish credibility through observing basic ethical and journalistic principles.
Document Type: Book
ICT4D – Connecting People for a Better World
Post date: 12 Mar 2007Offers some new and often surprising answers to the questions of wether information and communication technologies are effective instruments to improve lives OR just deepening already existing inequalities and divisions in the world.
Publication date: 31 Dec 2004
Document Type: Book
ICT4D – Connecting People for a Better World
Post date: 12 Mar 2007Offers some new and often surprising answers to the questions of wether information and communication technologies are effective instruments to improve lives OR just deepening already existing inequalities and divisions in the world.
Publication date: 31 Dec 2004
Document Type: Book
Examines the business dynamics and strategies used by firms that recognize the transformative power unleashed by the revolution of software platforms, a revolution that will change both new and old industries.
 Post date: 05 Oct 2007
Post date: 05 Oct 2007Examines the business dynamics and strategies used by firms that recognize the transformative power unleashed by the revolution of software platforms, a revolution that will change both new and old industries.
Moths to the Flame : The Seductions of Computer Technology
Post date: 28 Oct 2004Addresses important issues concerning the role of computers on privacy, war, and poverty.
Moths to the Flame : The Seductions of Computer Technology
Post date: 28 Oct 2004Addresses important issues concerning the role of computers on privacy, war, and poverty.
Online Privacy for Journalists
Post date: 29 Aug 2017A must-have guide for journalism in 2017. Topics include how to protect your source and sensitive data, maintaining your anonymity online, and securing your emails.
Online Privacy for Journalists
Post date: 29 Aug 2017A must-have guide for journalism in 2017. Topics include how to protect your source and sensitive data, maintaining your anonymity online, and securing your emails.
A concise introduction to open access, covers what open access is and isn't, how it benefits authors and readers of research, how it has moved from the periphery to the mainstream, and what its future may hold.
Publication date: 01 Jul 2012
License: Creative Commons Attribution-NonCommercial 3.0 Unported
Document Type: Book
 Post date: 27 Oct 2016
Post date: 27 Oct 2016A concise introduction to open access, covers what open access is and isn't, how it benefits authors and readers of research, how it has moved from the periphery to the mainstream, and what its future may hold.
Publication date: 01 Jul 2012
License: Creative Commons Attribution-NonCommercial 3.0 Unported Document Type: Book
Privacy on the Line: The Politics of Wiretapping and Encryption
Post date: 15 Nov 2016This book discusses the social function of privacy, how it underlies a democratic society, and what happens when it is lost. This updated edition covers recent controversies over NSA spying and other government threats to communications privacy.
Publication date: 01 Feb 2010
License: Standard Copyright License
Document Type: Book
Privacy on the Line: The Politics of Wiretapping and Encryption
Post date: 15 Nov 2016This book discusses the social function of privacy, how it underlies a democratic society, and what happens when it is lost. This updated edition covers recent controversies over NSA spying and other government threats to communications privacy.
Publication date: 01 Feb 2010
License: Standard Copyright License Document Type: Book
Software and Mind: The Mechanistic Myth and Its Consequences
Post date: 18 Apr 2016Addressing general readers as well as software practitioners, Software and Mind discusses the fallacies of the mechanistic ideology and the degradation of minds caused by these fallacies.
Publication date: 01 Jan 2013
License: Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International
Software and Mind: The Mechanistic Myth and Its Consequences
Post date: 18 Apr 2016Addressing general readers as well as software practitioners, Software and Mind discusses the fallacies of the mechanistic ideology and the degradation of minds caused by these fallacies.
Publication date: 01 Jan 2013
License: Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International
Taken Out of Context: American Teen Sociality in Networked Publics
Post date: 24 Mar 2009This dissertation documents author's 2.5-year ethnographic study of American teens' engagement with social network sites.
License: Creative Commons Attribution-NonCommercial-NoDerivs 3.0 Unported
Document Type: Thesis
Taken Out of Context: American Teen Sociality in Networked Publics
Post date: 24 Mar 2009This dissertation documents author's 2.5-year ethnographic study of American teens' engagement with social network sites.
License: Creative Commons Attribution-NonCommercial-NoDerivs 3.0 Unported Document Type: Thesis
The Digital Person - Technology and Privacy in the Information Age
Post date: 28 Mar 2008Aims to rethink longstanding notions of privacy to grapple with the consequences of living in an Information Age.
Publication date: 31 Dec 2004
License: Creative Commons Attribution-NonCommercial-NoDerivs 3.0 United States
The Digital Person - Technology and Privacy in the Information Age
Post date: 28 Mar 2008Aims to rethink longstanding notions of privacy to grapple with the consequences of living in an Information Age.
Publication date: 31 Dec 2004
License: Creative Commons Attribution-NonCommercial-NoDerivs 3.0 United States
The Future Does Not Compute, Transcending the Machines in Our Midst
Post date: 28 Oct 2004Reveals many reasons why we should not just accept the promises of a technological paradise without reflecting on its consequences.
The Future Does Not Compute, Transcending the Machines in Our Midst
Post date: 28 Oct 2004Reveals many reasons why we should not just accept the promises of a technological paradise without reflecting on its consequences.
The Future of Reputation - Gossip, Rumor, and Privacy on the Internet
Post date: 28 Mar 2008Shows how the free flow of information on the Internet can make us less free. Takes a journey through the ways in which private lives are being exposed online, and examines the implications.
Publication date: 24 Oct 2007
License: Creative Commons Attribution-NonCommercial-NoDerivs 3.0 United States
The Future of Reputation - Gossip, Rumor, and Privacy on the Internet
Post date: 28 Mar 2008Shows how the free flow of information on the Internet can make us less free. Takes a journey through the ways in which private lives are being exposed online, and examines the implications.
Publication date: 24 Oct 2007
License: Creative Commons Attribution-NonCommercial-NoDerivs 3.0 United States
The Hacker Crackdown: Law and Disorder on the Electronic Frontier
Post date: 28 Oct 2004A classic work highlights the 1990 assault on hackers, on the arrest of suspected illicit hackers and other computer-based law-breakers.
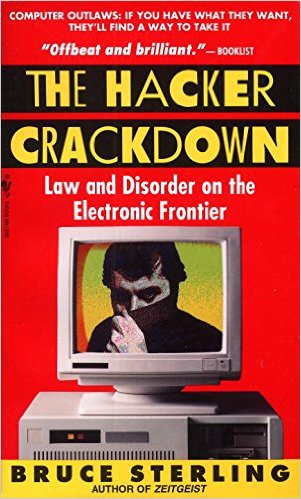
The Hacker Crackdown: Law and Disorder on the Electronic Frontier
Post date: 28 Oct 2004A classic work highlights the 1990 assault on hackers, on the arrest of suspected illicit hackers and other computer-based law-breakers.